Until recently, in our articles we have positioned PVS-Studio as a tool for detecting errors in code. While we almost never regarded PVS-Studio in a security context. We will try to remedy this situation and take a look at the tool in terms of testing of security applications and DevSecOps practices.
PVS-Studio is a static application security testing tool (SAST). In other words, the PVS-Studio analyzer detects not only typos, dead code and other errors, but also security weaknesses (potential vulnerabilities).
The tool works in Windows, Linux, macOS environments and analyzes program code written in C,C++ and C#. We're also planning to support the Java language by the end of 2018.
For the convenience of specialists who will use PVS-Studio as a SAST tool, the analyzer provides mappings for its warnings to Common Weakness Enumeration, SEI CERT Coding Standards, and also supports MISRA standard (currently in development).
Mapping tables of PVS-Studio diagnostics to different standards:
The most widespread classification of SAST tool warnings is Common Weakness Enumeration (CWE). Let's see, using the language of CWE, how the PVS-Studio analyzer helps to prevent vulnerabilities.
If we refer to a list of entries of publicly known information security vulnerabilities (CVE), it turns out that often the reason of vulnerabilities in applications is not any defects in the security system, but ordinary programming errors. National Institute of Standards and Technology (NIST) confirms this by stating that 64% of vulnerabilities in applications relate to errors in code.
It is such errors, described in CWE, that potentially can lead to vulnerabilities. Accordingly, if an error can be classified as CWE, it is possible that it may be exploited as a vulnerability and ultimately be added to the list of CVE. For clarity, we can use an image of the funnel:
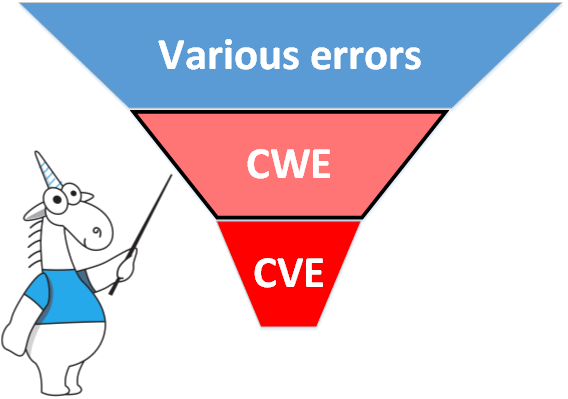
There is a great variety of errors. Some of them are dangerous from a security point of view and therefore are classified according to CWE. Some CWE-errors can be exploited and they represent vulnerabilities.
Indeed, in practice, only a very small part of discovered CWE-errors is dangerous and represents vulnerabilities. However, if you are developing security-critical applications and care about the security of users, you should consider these errors very seriously. Eliminating the CWE-errors, you protect your application from many vulnerabilities.
Now the relation between errors, PVS-Studio and vulnerabilities becomes apparent. PVS-Studio analyzer finds errors and classifies many of them as CWE. By fixing these errors, you make your application more reliable. The discovery of vulnerability in the product can seriously affect its reputation. By fixing the analyzer errors, you can significantly alleviate this risk at the earliest development stage - when you are writing the code.
PVS-Studio analyzer, like any other tool, does not guarantee that there are no vulnerabilities in your code. However, if PVS-Studio prevents, for example, 50% of potential vulnerabilities, this is wonderful.
Additionally we offer you to get acquainted with the article "How Can PVS-Studio Help in the Detection of Vulnerabilities?", showing the errors that led to vulnerabilities and which could have been avoided in case of using the PVS-Studio tool in the development process.
Start using PVS-Studio as a SAST solution: download PVS-Studio.
0